Set Up Single Sign-On
Allow users to sign in using their credentials from an external identity provider.
Set up single sign-on (SSO) to enhance security and simplify user access by allowing users to sign in with their existing credentials from an identity provider (IdP). Visier supports multiple SSO configurations including integration with multiple IdPs simultaneously. Visier supports IdP-initiated single sign-on processes, so any IdP that supports SAML 2.0 can be used. For more information, contact Technical Visier Support.
Note:
- You may need help from your IT administrator to set up single sign-on.
- We recommend that you set up a call with Visier Support to assist you through the SSO configuration. Users may be locked out if SSO is enabled with an invalid or untested configuration.
Set up single sign-on with your identity provider
Before you set up single sign-on, you will need to configure your SAML 2.0 settings with your IdP. Use the following information as guidance for configuring the SAML 2.0 assertion:
General settings
- Service Provider: Visier Analytics
- Service Provider Endpoint: https://vanityname.visier.com/VServer/auth
Note: Replace vanityname with your vanity URL domain.
- Single Logout Endpoint (Optional): https://vanityname.visier.com/VServer/auth/logoffWithSaml
Note:
- Replace vanityname with your vanity URL domain.
- This is required to enable single logout (SLO). If your IdP does not have a distinct setting to enable SLO, you can enable SLO by providing the above URL. To disable SLO in this case, just remove the SLO URL. If your IdP does have a setting to enable SLO, you must enable the setting and provide the above URL.
- Unique identifier for users: The NameID attribute should be mapped to the username field in Visier.
- Secondary information to be passed to Visier pertaining to user accounts: Nothing specific to user accounts, but we need to know the Issuer URL for SSO to work.
Security settings
The assertion must be signed with one of the following algorithms:
- RSA-SHA256
- RSA-SHA1
- DSA-SHA1
Tip: We recommend RSA-SHA256 as the signing algorithm because it is the most secure.
Issuer and certificate information
- NameID format expected by Visier: Standard format. This should be the username field in Visier, which is usually an email address. For example, john.doe@acmeinc.com
- NameIDPolicy: Unspecified, transient.
- Type of SSO initiation: IdP Initiated.
- Creation of user accounts: User accounts can be loaded from a file or created manually. Auto-provisioning is also available. For more information, see Auto Provisioning.
- Deactivation of user accounts: Deactivate user accounts via the solution.
- Self-signed certificates: Supported.
- SAML single logout: Supported. If enabled, users who sign out of their IdP site are also signed out of Visier.
- Session timeout limit: Yes. This can be adjusted in the SAML assertion. The following is an example of a three hour session:Copy
<saml2:SubjectConfirmationData NotOnOrAfter="2015-01-26T11:40:56.109Z" Recipient="https://vanityname.visier.com/VServer/auth"/>
</saml2:SubjectConfirmation>
</saml2:Subject>
<saml2:Conditions NotBefore="2015-01-26T08:40:56.109Z" NotOnOrAfter="2015-01-26T11:40:56.109Z">
Set up single sign-on in Visier
- On the global navigation bar, click Settings > Single Sign-On.
- Click Create New SSO Configuration in the upper-right corner of the SSO Configurations list.
- In the Create New SSO Configuration dialog, type the value found in the issuer claim within a SAML assertion, often referred to as the Entity ID in the Issuer box, and then click Create. The issuer uniquely identifies the identity provider within the solution and should match what was provided as part of the assertion during sign-on events. The Issuer cannot be changed. If you need to change this field, you will have to create a new configuration.
- In the SSO Configuration, enter the following information:
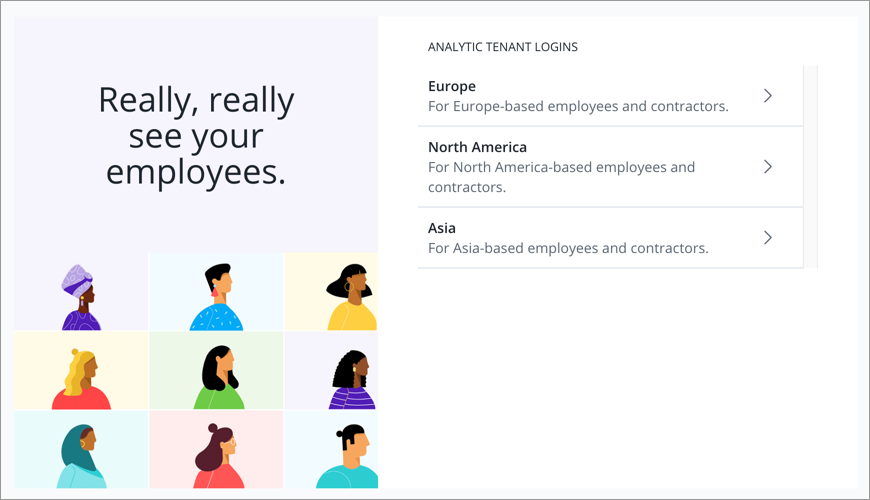
- Display name: The name of the SSO option that is shown to users on the Visier sign-in page when there are multiple SSO configurations.
- Description: Information about the SSO option that is shown to users on the Visier sign-in page when there are multiple SSO configurations. Provide a clear description to help users identify the right option. For more information, see Sign in with multiple SSO configurations.
- Login URL: The URL generated by the IdP that users will use to access Visier.
- Logout URL (Optional): The URL that users will be directed to after they sign out.
- Certificate: The X509 certificate that was used to sign the SAML assertion. SAML assertions should be signed but not encrypted.
- Issuer: The value found in the issuer claim within a SAML assertion, often referred to as the Entity ID. The issuer uniquely identifies the identity provider within Visier and should match what was provided as part of the assertion during sign-on events. This was provided when the configuration was created and cannot be changed.
- Parameters (Optional): Any additional parameters required by the IdP. These parameters must be URL encoded.
- Click Save to create the configuration.
-
Go back to the list of SSO configurations by clicking Single Sign-On in the navigation path at the top of the page.
- Optional: Create additional SSO configurations for different user groups or identity providers.
- Optional: Enable auto-provisioning to automatically create user accounts for new users who access Visier from your SSO portal. For more information, see Auto Provisioning.
- Optional: To exclude specific users from SSO, add users to the Bypass Users list. Selected users can bypass SSO and use their existing username and password to sign in to Visier with the following URL: https://{vanity-name}.visier.com/VServer/auth/admin. To complete the sign in process, users will be asked to enter a verification code that is sent via email.
Tip:
- To avoid being locked out while setting up SSO, we recommend adding an administrator to the Bypass Users list.
- Users who sign in to Visier with a username and password must verify their email address. Email validation does not apply to users who sign in to Visier with SSO.
- When finished, turn on the Enable SSO toggle.
Note: Contact Visier Technial Support to turn off SSO. If SSO is turned off, users need a Visier account and password to sign in. Users can reset their password from the sign-in page. However, they may require assistance with account setup and password resets.
Sign in with multiple SSO configurations
When multiple SSO configurations are available, the platform cannot always automatically determine the right configuration to use. In these cases, users are directed to a generic Visier page where they have to manually select the SSO configuration before they're redirected to the IdP URL. Clear display names and descriptions for each configuration will help users identify the right option.
Frequently asked questions
Is there a metadata file that can be consumed in our IdP to configure the integration?
No. There is no metadata file. However, the only Visier specific information needed to set up SSO with your identiy provider is the Service Provider Endpoint. You can find this in the IdP configuration in Studio by clicking Settings > Single Sign-On on the global navigation bar. The Service Provider Endpoint should be in the following format: https://vanityname.visier.com/VServer/auth
Is Just-in-Time (JIT) or SCIM provisioning supported?
Visier supports JIT provisioning. For more information, see Auto Provisioning. If auto provisioning is enabled, when a user attempts to sign into Visier, a user account will automatically be created for them if a username does not already exist matching the NameID sent. SCIM provisioning is supported in limited availability. For more information, see Set Up SCIM.
Is Multi-Factor Authentication (MFA) supported?
As an IdP-initiated connection, the sign in is initiated via the Identity Provider and any steps required by the end user as part of the authentication process is irrelevant from Visier’s perspective. Once any required steps are completed, the only requirement is that the IdP sends the SAML on to Visier.
Is a Sandbox/QA environment available to test the SSO integration prior to go-live?
No. We do not provide an environment for SSO testing.
How do users access Visier once SSO is set up?
When users navigate to the sign in page in their browser they will be seamlessly taken to the IdP to authenticate at the Login URL that you defined. Once authenticated, users will be redirected to Visier and signed in.
Once enabled can users only connect via SSO?
Exceptions can be made. For example, if you want to have a backup in case a certificate expires or there is an issue with the IdP. You may also have contractors that cannot be added to the IdP due to internal controls. In these cases, you can add users to the Bypass Users list when you set up SSO in Visier. It is a good idea to have an administrator on the list to avoid being locked out when you make changes to SSO. Bypass users can sign in to Visier independent of SSO. They will be redirected to a different sign in URL, enter their credentials, and asked to enter a verification code that is sent via email.
How can I troubleshoot if a user cannot sign in via the IdP?
When a user attempts to sign in to Visier via SSO, and is unsuccessful, there are two potential outcomes.
If the user is redirected to a generic Visier page requesting the user’s username and password, the request was passed on to Visier successfully via the IdP, but the SAML contents do not match what Visier expects. For example, the NameID sent does not match a user’s username in Visier, or the certificate or issuer sent does not match the expected values defined in Visier.
If the user encounters an error, or is redirected to a non-Visier landing page, the issue is on the IdP-side. Either the user is not configured to allow access to Visier (in the wrong user group) or an incorrect Login URL was entered in Visier to support IdP-initiated connections.
